
XTEA
Block cipher / From Wikipedia, the free encyclopedia
Dear Wikiwand AI, let's keep it short by simply answering these key questions:
Can you list the top facts and stats about XTEA?
Summarize this article for a 10 year old
SHOW ALL QUESTIONS
In cryptography, XTEA (eXtended TEA) is a block cipher designed to correct weaknesses in TEA. The cipher's designers were David Wheeler and Roger Needham of the Cambridge Computer Laboratory, and the algorithm was presented in an unpublished technical report in 1997 (Needham and Wheeler, 1997). It is not subject to any patents.[1]
This article includes a list of general references, but it lacks sufficient corresponding inline citations. (September 2015) |
Quick Facts General, Designers ...
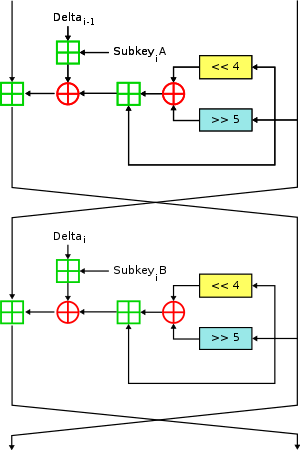 Two Feistel rounds (one cycle) of XTEA | |
| General | |
|---|---|
| Designers | Roger Needham, David Wheeler |
| First published | 1997 |
| Derived from | TEA |
| Successors | Corrected Block TEA |
| Cipher detail | |
| Key sizes | 128 bits |
| Block sizes | 64 bits |
| Structure | Feistel cipher |
| Rounds | variable; recommended 64 Feistel rounds (32 cycles) |
| Best public cryptanalysis | |
| A related-key rectangle attack on 36 rounds of XTEA (Lu, 2009)[vague] | |
Close
Like TEA, XTEA is a 64-bit block Feistel cipher with a 128-bit key and a suggested 64 rounds. Several differences from TEA are apparent, including a somewhat more complex key-schedule and a rearrangement of the shifts, XORs, and additions.